Implement Compliance Easily
Lacking know-how in IT security policies? With deeploi, policies are fulfilled automatically, audit-ready and secure.







200+ companies already trust deeploi
From innovative startups to long-established businesses
















Clarity Instead of Compliance Uncertainty
We translate complex compliance requirements into reliable IT standards
that are automatically enforced in day-to-day operations.

Information Security & Access Control
Protect sensitive data with role-based access control and MFA. Only authorized users can access critical systems and information.


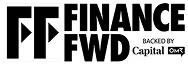
Malware Protection, Built In
Stop threats early. Security+ add-on provides real-time scans and malware protection, while MDM enforces policies and enables device monitoring and actions.
System Security & Activity Tracking
Maintain full visibility over devices, software, and security events. Stay transparent, audit-ready, and fully traceable at all times.


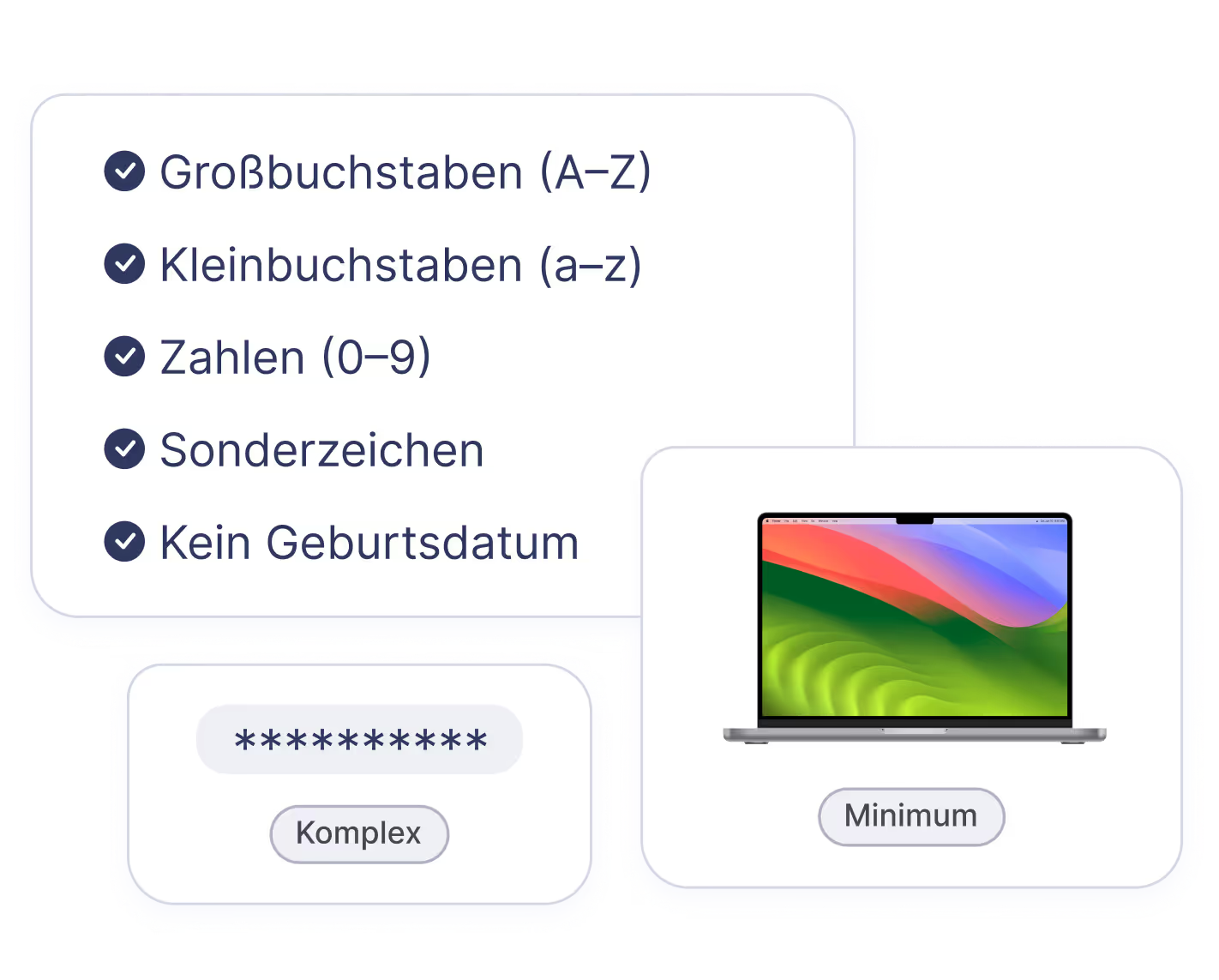
Strong Login. Strong Compliance
Secure access with multi-factor authentication for all platform logins and strict user permissions.
IT compliance in safe hands.
Built-In Security
Done Right
Encryption & Key Security
Devices use BitLocker or FileVault with secure key storage and verified access – ensuring strong data protection.

Asset & Device Management
Register devices, lock or wipe them when needed, and keep a clear overview of all hardware.

Complete Endpoint Protection: EPP + EDR
Stop threats with Security+ and SentinelOne. Real-time monitoring, behavioral analysis, and automated responses keep your endpoints secure.